Technology
Jememôtre: A Hidden Gem in the World of Contemparary Art
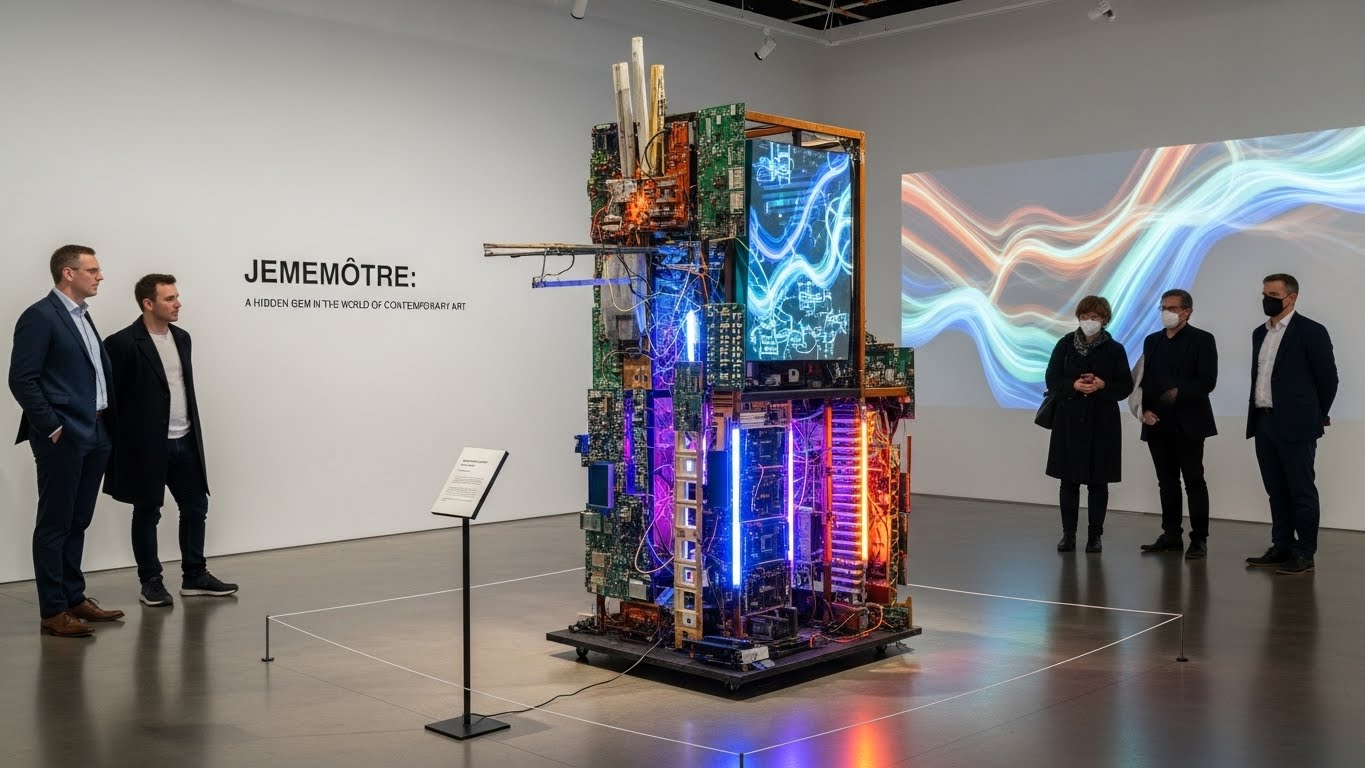
The term Jememôtre has gained rising attention across digital platforms, becoming an intriguing keyword in creative, cultural, and conceptual discussions. In this article, we explore the meaning, origin, and practical relevance of Jememôtre, providing a detailed and human-written breakdown for readers searching for clarity, insight, and actionable knowledge. Because Jememôtre is unique, its versatility makes it particularly interesting in modern content creation, idea development, and conceptual frameworks.
Understanding Jememôtre in Modern Language
What Jememôtre Represents in Contemporary Usage
The keyword Jememôtre often appears in conversations about identity, expression, and measurement of personal or creative value. While the word may not belong to traditional dictionaries, its conceptual depth gives it weight in modern discourse.
At its core, Jememôtre symbolizes:
-
A measure of self
-
A reflection of creativity
-
A conceptual tool for interpreting abstract ideas
-
A flexible linguistic element used in artistic communities
This makes not just a term, but a framework that helps individuals articulate complex thoughts and self-evaluation.
Origins and Evolution of Jememôtre
How Jememôtre Emerged as a Cultural Expression
The evolution of Jemeôtre can be traced to online communities exploring innovative vocabulary. Many emerging linguistic expressions originate from niche digital forums where creative experimentation is encouraged. Over time, has grown into a recognized conceptual keyword used by thinkers, writers, designers, and content creators.
A few key reasons for its popularity include:
-
Its memorable structure and phonetic harmony
-
Its ability to encapsulate multiple meanings
-
Its adaptable nature in creative contexts
In many communities, has become a symbolic reference to measuring one’s individuality or creative output.
The Functional Meaning of Jememôtre
Why Jememôtre Matters in Creative and Analytical Fields
The practical interpretation of varies depending on the field:
| Field | Interpretation of Jememôtre | Usage Example |
|---|---|---|
| Creativity | A tool to measure originality | Evaluating artistic direction |
| Psychology | A concept of personal awareness | Reflecting on self-identity |
| Education | A method for conceptual scoring | Activity assessment metrics |
| Digital Culture | A symbolic phrase in trends | Describing online personas |
This table shows how versatile is, functioning both symbolically and practically across various disciplines.
Jememôtre as a Tool for Personal Development
Applying Jememôtre to Enhance Self-Understanding
The concept of Jememtre can be used as a reflective practice. Individuals who apply the principles behind the term often use it to measure internal progress or evaluate their creative goals.
Key Applications of in Self-Development:
Key 1: Personal Measurement
Jememôtre represents a flexible scale that individuals can use to understand their growth patterns, strengths, and aspirations.
Key 2: Creative Benchmarking
Artists and writers use Jememtre to gauge originality and creative direction, helping determine whether their work aligns with their intended vision.
Key 3: Conceptual Reflection
Philosophically, serves as a mirror, allowing people to interpret complex emotions or intellectual frameworks.
This makes deeply relevant in personal journaling, emotional wellness evaluations, and artistic strategy planning.
Jememôtre in Digital Communication
How the Term Shapes Online Identity
In the digital age, words like Jemmôtre are powerful. They act as identity markers that help define how people express themselves. In many online communities, using niche conceptual words enhances personal branding and helps users stand out.
Digital creators adopt because:
-
It adds depth to posts or narratives
-
It conveys a sense of introspective creativity
-
It builds a personalized linguistic identity
When used strategically, Jemeôtre contributes to establishing a unique online presence that resonates with audiences seeking fresh perspectives.
Creative Interpretations of Jememôtre
Jememôtre in Art, Writing, and Design
Creatives frequently adopt conceptual vocabulary to structure their ideas. Jemmôtre has become popular in abstract writing and modern art discussions due to its versatility.
Art Perspective:
Artists may use to describe the emotional measure within their work—how much of themselves they put into each creation.
Writing Perspective:
Authors incorporate to give characters or themes greater introspective complexity.
Design Perspective:
Graphic designers may use the concept of when describing the balance, harmony, or personal imprint present in visual structures.
In each case, enriches the vocabulary of the creator while offering room for interpretation.
Jememôtre as a Cultural Symbol
Why the Concept Resonates Across Communities
Cultural expressions evolve through shared experiences. Jemmôtre has gained symbolic weight because it connects several themes:
-
Identity
-
Measurement
-
Creativity
-
Reflection
-
Originality
It represents a multilayered idea that individuals from different backgrounds can relate to without requiring strict definitions.
This universality makes Jememtre a memorable part of emerging cultural vocabulary.
How Jememôtre Supports Modern Problem-Solving
Conceptual Thinking Through Jememôtre
In creative problem-solving, abstract concepts often help push traditional boundaries provides a cognitive tool that encourages individuals to rethink their approach by evaluating components through a personalized measurement framework.
Examples include:
-
Examining emotional reactions
-
Evaluating project quality
-
Understanding team dynamics
-
Organizing conceptual tasks
By using as a guiding lens, individuals can build more intuitive and holistic solutions.
Incorporating Jememôtre Into Everyday Thinking
Practical Tips to Use Jememôtre Effectively
To make the most of the keyword Jemmôtre, consider applying it in these ways:
Key 4: Daily Reflection
Assign a personal score to tasks, moods, or progress to gain clarity.
Key 5: Creative Projects
Use Jememôtre to evaluate how closely a project aligns with your intended emotion or message.
Key 6: Communication
Integrate into conversations to add depth and conceptual understanding.
These applications show how can serve as a practical tool for everyday life.
Conclusion
The increasing relevance of Jememôtre demonstrates how modern culture continues to embrace creative and conceptual expressions. Its meaning is fluid yet powerful, offering individuals a unique way to interpret personal development, creativity, and communication. Whether used in writing, art, psychology, or digital identity, Jememôte stands out as a dynamic tool for understanding oneself and expressing internal perspectives with depth and clarity.
As the world continues to shift toward personalized expression and reflective thinking, will continue to play a vital role in shaping meaningful interactions and inspiring creative exploration.
Technology
GlobeInsightBlog: Your Go-To Source for Global Perspectives

GlobeInsightBlog stands as a dynamic platform designed to bring readers closer to the pulse of global developments. In an age where information is abundant but clarity is rare, GlobeInsightBlog offers a refreshing approach by combining depth, authenticity, and accessibility. Readers from different parts of the world turn to this platform to explore meaningful discussions that go beyond surface-level reporting. The goal is to provide a comprehensive understanding of events, ideas, and cultural movements shaping our interconnected world.
From emerging economies to technological revolutions, GlobeInsightBlog bridges gaps between regions and perspectives. It emphasizes storytelling that resonates with a global audience while remaining rooted in factual accuracy and thoughtful analysis. This unique combination ensures that readers not only stay informed but also develop a broader worldview. By focusing on quality over quantity, the platform continues to build trust and engagement among its growing readership.
The Vision Behind GlobeInsightBlog
The foundation of GlobeInsightBlog is built on the vision of creating a space where knowledge flows freely across borders. It aims to empower readers with insights that help them make informed decisions in both personal and professional spheres. By addressing complex global topics in a simplified manner, the platform ensures accessibility without compromising on depth or accuracy. This vision reflects a commitment to intellectual curiosity and cultural understanding.
At its core, GlobeInsightBlog values diversity in thought and expression. Contributors from various backgrounds bring unique perspectives that enrich the overall content experience. This collaborative approach allows the platform to present balanced viewpoints on global issues. As a result, readers gain exposure to ideas that challenge assumptions and encourage critical thinking in an ever-changing world.
Content Diversity on GlobeInsightBlog
One of the defining features of GlobeInsightBlog is its diverse range of topics. The platform covers areas such as global politics, economic trends, technological innovation, cultural evolution, and environmental sustainability. This wide spectrum ensures that readers can explore multiple dimensions of global life in one place. Each topic is approached with a focus on clarity, relevance, and real-world impact.
The content is carefully curated to maintain consistency in quality while offering variety in perspective. Whether it is an in-depth analysis of international trade or a reflective piece on cultural traditions, GlobeInsightBlog delivers value through well-researched articles. This diversity not only keeps readers engaged but also encourages them to explore subjects beyond their usual interests, broadening their intellectual horizons.
How GlobeInsightBlog Enhances Global Awareness
GlobeInsightBlog plays a crucial role in enhancing global awareness by presenting information in a context that is both informative and relatable. It connects local events to global trends, helping readers understand how different regions influence one another. This interconnected approach fosters a deeper appreciation of the complexities involved in global interactions.
By highlighting stories from underrepresented regions, GlobeInsightBlog ensures that diverse voices are heard. This inclusive approach allows readers to gain insights into cultures and perspectives they may not encounter elsewhere. As a result, the platform contributes to a more informed and empathetic global community, where understanding replaces misconceptions.
Editorial Approach and Quality Standards
The editorial process of GlobeInsightBlog is centered around accuracy, originality, and readability. Each article undergoes thorough research and careful editing to ensure that it meets high standards of quality. The platform prioritizes authenticity, ensuring that all content is free from plagiarism and reflects genuine human insight.
In addition to maintaining accuracy, GlobeInsightBlog focuses on engaging storytelling. Articles are structured to guide readers through complex topics in a logical and compelling manner. This approach not only enhances readability but also ensures that readers remain engaged from beginning to end, making the learning experience both enjoyable and informative.
Global Trends and Insights on GlobeInsightBlog
GlobeInsightBlog serves as a valuable resource for understanding global trends that shape the future. From technological advancements to shifts in economic policies, the platform provides in-depth analysis that helps readers stay ahead of the curve. These insights are presented in a way that is both accessible and actionable.
The platform also explores the implications of these trends on everyday life. By connecting macro-level developments to individual experiences, GlobeInsightBlog ensures that its content remains relevant to a wide audience. This practical approach allows readers to apply their knowledge in real-world scenarios, enhancing the overall value of the information provided.
Cultural Exploration Through GlobeInsightBlog
Cultural exploration is a key aspect of GlobeInsightBlog, offering readers a window into the traditions, values, and lifestyles of different communities. Through detailed narratives and thoughtful analysis, the platform highlights the richness and diversity of global cultures. This approach fosters a deeper understanding of cultural nuances and shared human experiences.
The platform also addresses the impact of globalization on cultural identities. By examining how cultures evolve and adapt, GlobeInsightBlog provides insights into the dynamic nature of human societies. This exploration not only educates readers but also promotes respect and appreciation for cultural diversity in a rapidly changing world.
Technology and Innovation Insights
Technology plays a significant role in shaping the modern world, and GlobeInsightBlog provides comprehensive coverage of this ever-evolving field. The platform explores innovations that influence industries, economies, and daily life. By breaking down complex technological concepts, it ensures that readers can easily understand their significance.
In addition to highlighting advancements, GlobeInsightBlog examines the challenges associated with technological growth. Topics such as data privacy, digital transformation, and ethical considerations are discussed in detail. This balanced approach allows readers to gain a holistic understanding of technology’s impact on society.
Sample Insight Table on GlobeInsightBlog Topics
| Category | Focus Area | Reader Benefit |
|---|---|---|
| Global Politics | Policy and diplomacy | Better understanding of governance |
| Technology | Innovation trends | Awareness of digital transformation |
| Culture | Traditions and lifestyles | Broader cultural appreciation |
| Economy | Market analysis | Insight into financial trends |
| Environment | Sustainability | Knowledge of ecological issues |
This table illustrates how GlobeInsightBlog organizes its content to deliver targeted insights across various domains. Each category is designed to provide specific value to readers, ensuring a comprehensive learning experience.
Building a Community Through GlobeInsightBlog
GlobeInsightBlog is more than just a content platform; it is a community of thinkers, readers, and contributors. It encourages interaction and dialogue among its audience, creating a space where ideas can be shared and discussed. This sense of community enhances the overall experience, making it more engaging and meaningful.
The platform also supports collaboration by inviting contributions from experts and enthusiasts alike. This inclusive approach allows for a diverse range of voices, enriching the content and fostering a sense of belonging among readers. As a result, GlobeInsightBlog continues to grow as a vibrant hub for global perspectives.
Another Insight Table Highlighting Reader Engagement
| Feature | Purpose | Outcome |
| Expert Articles | Provide depth | Increased credibility |
| Reader Contributions | Encourage participation | Stronger community engagement |
| Interactive Content | Enhance experience | Higher reader retention |
| Global Topics | Expand knowledge | Broader audience reach |
This table demonstrates how GlobeInsightBlog integrates various features to create an engaging and informative platform. Each element contributes to a richer user experience, ensuring that readers remain connected and invested.
Future of GlobeInsightBlog in a Globalized World
As the world becomes increasingly interconnected, the role of platforms like GlobeInsightBlog becomes even more significant. The platform is poised to expand its reach by embracing new technologies and innovative content formats. This forward-thinking approach ensures that it remains relevant in an ever-changing digital landscape.
Looking ahead, GlobeInsightBlog aims to continue its mission of providing reliable and insightful content. By staying true to its core values of quality and authenticity, it will continue to serve as a trusted source for global perspectives. This commitment to excellence ensures that the platform will remain a valuable resource for years to come.
Conclusion
GlobeInsightBlog distinguishes itself through its dedication to quality, diversity, and global understanding. It offers a unique blend of insightful analysis and engaging storytelling, making it a go-to platform for readers seeking meaningful content. By addressing a wide range of topics, it ensures that there is something for everyone.
Ultimately, GlobeInsightBlog succeeds because it connects people through knowledge and shared understanding. It empowers readers to explore the world from different perspectives, fostering a sense of curiosity and awareness. As a result, it continues to build a loyal audience that values depth, authenticity, and global insight.
Technology
Anuwave: How This Innovative Solution is Transforming Industries
Technology
FlagshipAcc.com: Your Ultimate Guide to Premium Accounts
-
 Blog2 months ago
Blog2 months agoSimpcit6: Redefining Simplicity in a Complex World
-
 Blog7 months ago
Blog7 months agoBaddi Hub: An Emerging Industrial and Business Hotspot
-
 Technology6 months ago
Technology6 months agoYourAssistantLive com: The Future of Smart Digital Assistance
-

 food7 months ago
food7 months agoCalamariere: How to Perfectly Prepare at Home
-

 Health5 months ago
Health5 months agoNerovet AI Dentistry: Enhancing Patient Experience and Treatment Outcomes Dental Care
-

 Technology2 months ago
Technology2 months agoVoomixi com: The Digital Platform Redefining Online Interaction
-

 Technology6 months ago
Technology6 months agoAnonibs: The Trending Anonymous Image Board Platform
-

 Business4 months ago
Business4 months agoTop Benefits of Using Quality Wire Rope Lube in US Heavy Industry


