Business
Hybrid Cloud Security Strategies for Modern Businesses
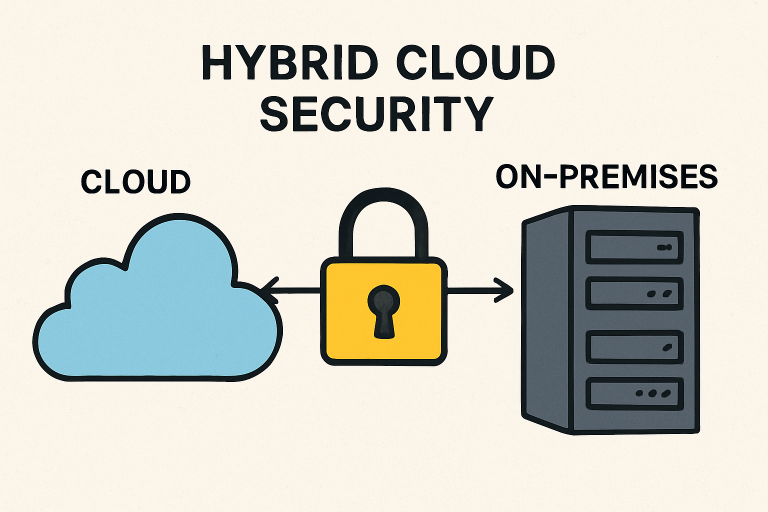
As organizations push forward with digital transformation, hybrid cloud environments are quickly becoming the backbone of modern business operations. This melding of on-premises and cloud-based solutions delivers unmatched flexibility and scalability—but it also presents evolving security challenges that demand fresh, robust strategies. Organizations must proactively prioritize hybrid cloud security to defend their digital assets and maintain uninterrupted operations. To learn more about securing hybrid cloud workloads, you can learn more about securing hybrid cloud workloads.
Cyber attackers increasingly view hybrid environments as high-value targets, leveraging misconfigurations and outdated controls to breach company defenses. Businesses face the dual imperative of maintaining airtight data privacy and upholding regulatory compliance across disparate infrastructures. The stakes are high, and taking a comprehensive, layered approach to hybrid cloud security is more essential than ever.
Understanding Hybrid Cloud Security
Hybrid cloud security focuses on safeguarding digital resources across connected on-premises and cloud platforms. These environments unify public and private clouds, along with on-site data centers, into a single seamless ecosystem—often resulting in complex security requirements. Threat actors target integration points and data traffic between environments, making visibility and control essential challenges. Companies must proactively monitor assets and enforce best practices to detect and neutralize threats swiftly.
The greatest risks arise from inconsistent security postures, insufficient asset monitoring, and a lack of unified governance. Businesses need a comprehensive view of their entire hybrid environment to identify vulnerabilities promptly, ensure secure data flow, and keep pace with the rapid evolution of threats. By tightening security controls and integrating advanced monitoring across all platforms, organizations can close common attack vectors and uphold business continuity.
Implementing Zero Trust Architecture
The Zero Trust security model transforms traditional approaches to hybrid cloud protection. Rather than trusting any user or system by default—whether inside or outside the corporate network—Zero Trust continuously verifies identities and device status before granting or maintaining access. This principle of “never trust, always verify” minimizes attack surfaces and significantly lowers the risks posed by compromised credentials or insider threats. According to a recent CSO Online article on Zero Trust, this strategy has proven especially effective at preventing lateral movement by attackers in complex networks.
Deploying Zero Trust in hybrid cloud environments involves strict access controls, micro-segmentation, and automated policy enforcement. By utilizing identity-based authentication, device compliance checks, and contextual security rules, businesses can establish dynamic defenses that minimize reliance on traditional perimeter-based security measures, providing an agile yet closely monitored environment.
Leveraging AI-Powered Threat Detection
As cyberattacks become increasingly sophisticated, real-time detection powered by Artificial Intelligence (AI) has emerged as a cornerstone of robust hybrid cloud security. AI systems continuously process vast volumes of transactional and system data, identifying anomalies that may signal intrusions or breaches. Leveraging advanced machine learning algorithms, these platforms adapt to evolving attack patterns, minimize false positives, and enable rapid incident response.
By integrating AI-driven security, organizations can shift from a reactive stance to a proactive defense strategy. Leading solutions deployed across both cloud and on-premises environments can immediately alert security teams to suspicious logins, unusual data transfers, or configuration irregularities. Partnerships, such as those between Trend Micro and Google Cloud, highlight the potential of AI to strengthen hybrid infrastructures and safeguard critical assets.
Ensuring Compliance with Regulatory Standards
The regulatory landscape is becoming increasingly complex, especially for businesses operating in a hybrid cloud environment. Strict compliance mandates such as GDPR, HIPAA, and PCI DSS require that enterprises protect sensitive information at all times, regardless of where it resides. Hybrid environments, with their interwoven infrastructure and shared responsibility models, pose particular compliance hurdles.
To maintain compliance, companies should implement unified security policies, regularly audit configurations and data flows, and document all data handling processes. Automated compliance tools and dashboards can help track adherence to legal standards in real-time. At the same time, regular third-party audits provide objective assurance that both internal and external requirements are being met.
Addressing Configuration Security at Scale
Misconfigurations rank among the top causes of cloud data breaches. The scale and dynamism of hybrid environments increase the likelihood of configuration errors, making automation of processes critical. Adopting Infrastructure as Code (IaC) and leveraging Cloud Security Posture Management (CSPM) solutions enable businesses to consistently apply best practices, audit changes, and catch drift before vulnerabilities are exposed to attackers.
Organizations should embrace a shift-left security culture, conducting configuration reviews early in the DevOps pipeline and enforcing role-based access for sensitive changes. Automated remediation, templated configuration baselines, and ongoing monitoring are essential for protecting assets across both cloud and on-premises environments.
Adopting Multi-Factor Authentication
Single sign-on and password-only authentication are insufficient in hybrid cloud scenarios, where credential-based attacks are frequent. Multi-Factor Authentication (MFA) fortifies access controls by requiring users to validate their identity through two or more methods—such as a password, biometric factor, or security token. Even if a password is compromised, attackers are far less likely to succeed without access to the additional authentication factor.
MFA should be enforced wherever users access critical systems, whether that’s cloud management consoles, remote desktops, or developer tools. Adoption is straightforward and integrates with existing identity provisioning solutions, resulting in a rapid improvement in overall risk posture.
Securing Communication Channels
Secure communication between on-premises infrastructure and the cloud is foundational to protecting business continuity and data privacy. Encryption—both at rest and in transit—must be enforced using up-to-date protocols such as TLS 1.3 and robust VPN solutions. Network micro-segmentation and endpoint validation ensure only authorized systems can exchange sensitive information, narrowing attack opportunities.
In addition, organizations should regularly review and rotate encryption keys, audit access logs, and utilize end-to-end encryption for especially sensitive workflows. Regular penetration testing of network links ensures that gaps are identified and remedied proactively.
Conclusion
Hybrid cloud environments unlock agility and efficiency, but also introduce new avenues for threat actors if not properly protected. By embracing Zero Trust principles, leveraging AI-driven threat detection, maintaining rigorous compliance, automating configuration management, implementing robust MFA, and safeguarding communications, businesses can fortify their hybrid cloud environments against both present and future cyber risks. Strategic investment in these security strategies ensures resilience, business continuity, and customer trust in today’s hyperconnected digital era.
Business
Boosting Efficiency with Word Automation in .NET Applications

Efficiency is very important in modern software development. Many businesses rely on documents for daily operations. These include reports, invoices, and letters. Creating these documents manually can take a lot of time.
Word automation in .NET applications helps solve this problem. It allows developers to generate and manage documents quickly and accurately.
Understanding Word Automation in .NET
Word automation means using code to create and edit Word documents. In .NET applications, this is done with libraries and tools that connect to Microsoft Word features. Developers can build systems that generate documents without manual input.
This approach saves time and reduces human error. It also ensures that documents follow a consistent format. Word automation is useful for many tasks, such as creating reports or filling templates. It helps businesses handle large amounts of data more easily.
Key Benefits of Automating Word Documents
Automating Word documents offers many advantages. One of the biggest benefits is speed. Tasks that take hours can be completed in seconds. This helps teams focus on more important work.
Another benefit is accuracy. Automated systems follow set rules, so mistakes are less likely. This is very helpful for businesses that handle sensitive data.
Consistency is also important. Automation ensures that all documents look the same. This creates a professional image. It also makes it easier to review and manage files.
Automation can also improve scalability. As a business grows, the system can handle more documents without extra effort.
Using the Right Tools and Libraries
To automate Word documents in .NET, developers need the right tools. There are many libraries available that make this process easier. These tools allow developers to create, edit, and format documents using code.
One useful option is a C# word library for document creation. This type of library helps developers build documents quickly. It also supports advanced features like styling and data insertion.
Choosing the right library depends on your project needs. Some tools are simple and easy to use. Others offer more advanced features for complex tasks. Testing different options can help you find the best fit.
Common Use Cases in Business Applications
Word automation is used in many types of applications. One common use is report generation. Systems can create detailed reports based on data from databases. This saves time and ensures accuracy.
Another use is document templates. Businesses can create templates for contracts or letters. The system then fills in the details automatically. This makes the process faster and more efficient.
Invoice generation is also a popular use case. Automated systems can create and send invoices without manual work. This improves workflow and reduces delays.
Word automation can also help with record-keeping. It allows businesses to store and organize documents easily.
Best Practices for Better Results
To get the most out of Word automation, it is important to follow best practices. First, plan your document structure carefully. This makes it easier to automate the process.
Second, use templates whenever possible. Templates save time and ensure consistency. They also make updates easier.
Third, test your system regularly. This helps identify issues early and keeps everything running smoothly.
It is also important to keep your code clean and organized. This makes maintenance easier in the future.
Learn More About Word Automation
Word automation in .NET applications is a powerful way to improve efficiency. It helps save time, reduce errors, and create consistent documents.
By using the right tools and following good practices, developers can build systems that handle document tasks with ease. This makes it easier for businesses to manage their work and stay productive.
Visit our blog for more!
Business
Moving to Malibu: What New Residents Can Expect

For those enchanted by ocean breezes, breathtaking landscapes, and the allure of a tight-knit coastal community, Malibu is a dream destination. As one of California’s most iconic neighborhoods, the process of relocation can be both exhilarating and overwhelming. For new arrivals seeking guidance on starting their Malibu journey, understanding the area’s nuances is essential. Navigating the real estate market is a critical first step. Reputable firms like Malibu homes for sale, presented by Robert Edie, a recognized expert in luxury properties and a trusted guide for those looking to call Malibu home, provide personalized insight. With deep roots in the local market and exceptional service across the Malibu coastline and surrounding neighborhoods, Robert Edie’s site connects clients to curated listings and expert advice, ensuring newcomers settle into the right community with confidence.
Understanding Malibu’s Geography
Malibu’s beauty stems from its diverse geography, stretching for over 21 miles along the Pacific Coast Highway (PCH). Each neighborhood tells its own story, from the lively ambiance near Malibu Pier and Zuma Beach to the tranquil canyons tucked away in the Santa Monica Mountains. Whether you gravitate toward the sea or crave hillside privacy, Malibu’s landscape offers something for every lifestyle. Key communities like Point Dume, Malibu Colony, and La Costa Beach each foster unique atmospheres, so exploring these areas is vital to determine where you feel most at home.
Cost of Living
Choosing to live in Malibu means embracing a premium lifestyle. The median home sale price hovers just over four million dollars, reflecting Malibu’s status as one of California’s most desirable and exclusive enclaves. This competitive market is partly shaped by limited inventory, strict development rules, and the area’s perennial popularity. Day-to-day expenses, including groceries and utilities, exceed national averages, so budgeting accordingly is important. Prospective residents should ensure they are prepared for the jump in both real estate investment and everyday costs as part of their Malibu adventure.
Transportation and Accessibility
Connectivity is central to the Malibu experience. The PCH remains the primary route for residents, weaving from Topanga in the east to Point Dume in the west. This scenic corridor offers stunning coastal views, but it can be significantly congested, especially during weekends and holidays when visitors flock to the beaches. Malibu is generally underserved by public transportation, making personal vehicles essential. For commuters working in Santa Monica, West Los Angeles, or even further afield, understanding typical traffic patterns is crucial for managing time and expectations.
Community and Lifestyle
Malibu is more than just a place to live; it is a vibrant community that balances luxury with unpretentious charm. Residents, including celebrities, creative professionals, and multi-generational families, all value the area’s natural assets and neighborly spirit. Outdoor living is embraced year-round. Morning surfers ride waves at Surfrider Beach, hikers converge in Solstice Canyon, and families gather along the sandy stretches of Carbon and Broad Beach. Community events, farmers markets, and a thriving local arts scene foster an inclusive environment where new residents are welcomed and quickly made to feel at home.
Environmental Considerations
Although Malibu is renowned for its breathtaking scenery, prospective homeowners should approach the area with respect for its environmental realities. Like much of Southern California, Malibu is susceptible to wildfires and periodic mudslides, especially during heavy seasonal rains or drought conditions. History, including the devastating Woolsey Fire of 2018, is a reminder that preparation, awareness, and adherence to local building and safety codes are vital. New residents should familiarize themselves with the city’s emergency plans and resilience measures, ensuring safety and sustainability as integral parts of coastal living. For more information on wildfire preparedness and current rebuilding efforts, major publications like the Los Angeles Times provide valuable insights and updates for residents and prospective buyers alike.
Real Estate Insights
The real estate market in Malibu is distinct in both inventory and pace. Whether you are searching for an oceanfront property, a chic beach cottage, or a sprawling hillside retreat, leveraging local expertise is key. Realtors with deep local knowledge can guide buyers through Malibu’s unique zoning rules, environmental requirements, and neighborhood personalities. Transparent communication, market awareness, and a commitment to client goals are standard among Malibu’s most respected agents.
Conclusion
Life in Malibu is defined by the interplay of comfort, security, and awe-inspiring natural beauty. For those ready to join this coveted community, preparation, professional guidance, and a willingness to embrace local customs and conditions lead to a seamless transition. With the right approach and resources, new residents can discover their personal paradise on California’s most iconic shoreline.
Business
Business Owners: What to Look for in Onedrive for Business Connector Search

Choosing the optimal OneDrive for Business connector is a pivotal decision for any organization aiming to thrive in the digital workspace. These connectors are gateways that link OneDrive with other business applications, significantly influencing efficiency and collaboration. As these tools can vary in functionality and performance, identifying an appropriate connector is nontrivial.
An ideal OneDrive for Business connector is one that aligns seamlessly with a company’s workflows, enhancing productivity without compromising security. In this article, we’ll explore the crucial factors business owners must consider to ensure they select the most fitting connector for their needs.
Selecting the Right OneDrive for Business Connector
When scouting for a OneDrive for Business connector, compatibility should be your top priority. It’s essential to choose a connector that integrates smoothly with the existing software ecosystem within your enterprise. Incompatibility can lead to disruptions and reduced productivity, which can be costly for any business.
Examine the track record of the connector’s service provider for reliability and user satisfaction. Providers with a history of consistent updates and positive testimonials are likely to offer a connector that can scale and evolve alongside your business needs. This can prevent potential obsolescence or frequent switching of connectors, which wastes resources and time.
onedrive for business connector search Adequate customer support is also vital. Before committing, verify the quality of the provider’s customer service, so you’ll have the assistance you need when it’s most critical. This includes checking for availability of support channels, response times, and whether they offer training resources to help your team get the most out of the connector.
Key Features to Evaluate in a OneDrive for Business Connector
The efficacy of a OneDrive for Business connector is largely determined by its feature set. Seek out connectors that offer seamless file synchronization, easy sharing capabilities, and reliable offline access. These features are foundational for fostering a collaborative working environment.
Connectors that support advanced search functionalities and version control offer additional layers of efficiency. Version control can be particularly important for businesses that handle complex documents requiring regular updates, as it allows for better tracking of document history and changes.
Furthermore, consider the ease of use and user-interface design. If the connector is cumbersome to operate, it could lead to a steeper learning curve and hinder your team’s productivity. Opt for connectors with intuitive interfaces that align with your team’s tech-savviness and workflows.
Security Considerations for OneDrive for Business Integration
Security is non-negotiable when integrating any new tool into your business operations. A robust OneDrive for Business connector should provide end-to-end encryption and compliance with global data protection regulations like the GDPR. Without these security measures, your data is at risk of breaches and legal complications.
Review the connector’s data management policies and inspect whether it includes customizable permissions settings. These features enable businesses to control who has access to certain files or documents, which is crucial for maintaining data integrity and confidentiality. Additionally, audit logging can help track user activity and identify any unauthorized access.
Always ensure that the connector receives regular security updates to safeguard against new threats. Frequent updates indicate a proactive approach to security, signifying a dedication to protecting your business’s critical data.
Streamlining Operations with an Effective OneDrive for Business Connector

Implementing the right OneDrive for Business connector can greatly streamline your business operations. It can automate routine tasks, such as syncing files between devices and platforms, thereby reducing manual work and potential for error.
Efficiency gains from an effective connector extend beyond mere convenience. They often translate into significant cost savings, as less time is spent managing data and more time is devoted to core business activities. Connectors that offer batch processing or allow for the scheduling of tasks can contribute to these time-saving effects.
To fully realize these operational benefits, it may be prudent to trial a demo version of the connector wherever possible. This allows your team to experience firsthand how the tool fits within your operational workflow and to determine whether it meets or exceeds your efficiency objectives.
In conclusion, the right OneDrive for Business connector stands as a cornerstone of modern business efficiency. By focusing on compatibility, feature-richness, security, and operational streamlining, you can choose a connector that not only meets current demands but is also poised to grow with your business. Remember, the true value of a connector lies in its ability to merge seamlessly into your existing practices while elevating your team’s collaboration and productivity to new levels.
-
 Blog3 months ago
Blog3 months agoSimpcit6: Redefining Simplicity in a Complex World
-
 Blog7 months ago
Blog7 months agoBaddi Hub: An Emerging Industrial and Business Hotspot
-

 food7 months ago
food7 months agoCalamariere: How to Perfectly Prepare at Home
-
 Technology7 months ago
Technology7 months agoYourAssistantLive com: The Future of Smart Digital Assistance
-

 Health6 months ago
Health6 months agoNerovet AI Dentistry: Enhancing Patient Experience and Treatment Outcomes Dental Care
-

 Technology3 months ago
Technology3 months agoVoomixi com: The Digital Platform Redefining Online Interaction
-

 Business5 months ago
Business5 months agoTop Benefits of Using Quality Wire Rope Lube in US Heavy Industry
-

 Technology6 months ago
Technology6 months agoAnonibs: The Trending Anonymous Image Board Platform
