Technology
Lkmschromebookcheck: Unlocking the Power of LKM for Your Chromebook
Lkmschromebookcheck represents a forward-thinking approach to maximizing the potential of Chromebooks through the strategic use of Loadable Kernel Modules. In today’s rapidly evolving digital environment, Chromebooks have become popular for students, professionals, and businesses due to their simplicity, speed, and security-focused architecture. Built primarily around ChromeOS, these lightweight devices emphasize cloud-based productivity and streamlined performance. However, as user needs expand beyond basic browsing and document editing, the demand for deeper customization and enhanced hardware interaction has grown significantly.
This is where Lkmschromebookcheck becomes relevant. By focusing on kernel-level enhancements, it offers a conceptual pathway to unlocking advanced functionality without compromising system integrity. Chromebooks are powered by the Linux kernel at their core, and Loadable Kernel Modules, often abbreviated as LKM, allow specific features to be added or removed dynamically. Understanding this relationship is essential for anyone seeking to explore performance optimization, advanced hardware compatibility, and development flexibility within a Chromebook environment.
Understanding the Foundation Behind Lkmschromebookcheck
To fully appreciate the significance of Lkmschromebookcheck, it is important to understand what Loadable Kernel Modules actually are. LKMs are pieces of code that can be loaded into the kernel at runtime. Instead of rebuilding the entire operating system, users and developers can insert modules that extend functionality such as hardware drivers, file system support, or network capabilities.
Chromebooks, while secure and streamlined, are intentionally restricted to maintain simplicity and protect users from instability. The architecture of ChromeOS is designed to limit deep system modifications. However, the underlying Linux-based structure provides theoretical flexibility for advanced users who enable developer mode. Lkmschromebookcheck addresses this balance between control and caution by focusing on responsible and informed module management.
The relationship between ChromeOS and the Linux kernel creates a unique ecosystem. Unlike traditional Linux distributions, ChromeOS restricts root-level access under standard conditions. When users explore development pathways, kernel modules must be carefully managed to prevent security vulnerabilities. Lkmschromebookcheck emphasizes structured evaluation and compatibility assessment before introducing kernel-level changes.
How Lkmschromebookcheck Enhances Chromebook Performance
Performance optimization is one of the primary motivations behind exploring LKM integration on Chromebooks. While these devices are efficient for everyday tasks, certain workloads such as development environments, virtualization, and specialized hardware connections may require additional support.
Lkmschromebookcheck focuses on analyzing system requirements and aligning module integration with device architecture. For example, when enhanced hardware acceleration or experimental driver support is needed, Loadable Kernel Modules can provide a controlled method of implementation. Rather than modifying the entire system image, modules allow incremental adjustments that can be reversed if necessary.
The table below illustrates how kernel-level customization compares to standard system configurations:
| Feature Area | Standard Chromebook Setup | With LKM Integration |
|---|---|---|
| Hardware Drivers | Pre-installed official drivers | Custom or experimental drivers possible |
| File System Support | Limited to supported formats | Expanded file system compatibility |
| Network Tools | Basic networking stack | Advanced networking modules |
| Development Capabilities | Crostini container support | Deeper kernel-level experimentation |
This structured comparison demonstrates how Lkmschromebookcheck can expand capabilities while preserving the core reliability that Chromebooks are known for.
Security Considerations Within Lkmschromebookcheck
Security is one of the defining strengths of Chromebooks. Verified boot, sandboxing, and automatic updates are fundamental pillars of ChromeOS design. Introducing kernel modules must be handled with extreme care because the kernel operates at the highest privilege level within the system.
Lkmschromebookcheck approaches security from a proactive standpoint. Kernel modules, if improperly written or sourced from unverified repositories, can introduce vulnerabilities. For this reason, evaluation, source verification, and compatibility testing are essential before any module integration.
Security comparison highlights the importance of controlled implementation:
| Security Aspect | Default ChromeOS | With Careful LKM Use |
|---|---|---|
| Verified Boot | Fully enforced | May require developer adjustments |
| System Integrity | Locked by default | Requires responsible management |
| Attack Surface | Minimal | Potentially expanded if misconfigured |
| Update Stability | Automatic | Must ensure module compatibility |
By maintaining awareness of these variables, Lkmschromebookcheck promotes informed experimentation rather than reckless modification.
Developer Mode and Lkmschromebookcheck Integration
Developer mode is a necessary step for anyone seeking to explore kernel-level enhancements on a Chromebook. Activating this mode removes certain security restrictions and allows deeper system access. However, it also disables verified boot warnings and may increase exposure to risk.
Lkmschromebookcheck emphasizes structured evaluation before enabling developer mode. Understanding device compatibility, firmware limitations, and recovery procedures is critical. Chromebooks are manufactured by various brands, each with slightly different hardware implementations, which can influence module compatibility.
When developer mode is active, users gain access to advanced terminal commands and system directories. This environment enables experimentation with Loadable Kernel Modules while still retaining the option to revert to default configurations if needed.
Hardware Compatibility and Lkmschromebookcheck
One of the strongest applications of LKM exploration involves hardware compatibility. While Chromebooks support a wide range of peripherals, some specialized devices may not be recognized out of the box. In Linux-based systems, additional kernel modules often provide extended driver support.
Lkmschromebookcheck encourages structured testing of hardware modules before deployment. This includes analyzing chipset compatibility, verifying kernel version alignment, and ensuring module signing requirements are met. Since ChromeOS updates can modify kernel versions, maintaining compatibility requires continuous evaluation.
The table below illustrates potential compatibility improvements:
| Hardware Type | Default Support | Extended Support via LKM |
|---|---|---|
| External WiFi Adapters | Limited models | Broader chipset support |
| USB Serial Devices | Partial recognition | Full serial communication modules |
| Experimental Storage Devices | Restricted | Additional file system modules |
| Development Boards | Basic | Custom driver integration |
By applying careful compatibility checks, Lkmschromebookcheck enables advanced connectivity without sacrificing system reliability.
System Stability and Maintenance Under Lkmschromebookcheck
System stability remains a central concern when modifying kernel components. Loadable Kernel Modules operate at a critical level of the operating system, meaning that errors can cause crashes or unpredictable behavior.
Lkmschromebookcheck advocates incremental deployment. Instead of integrating multiple modules simultaneously, each change should be tested independently. Monitoring system logs, performance benchmarks, and boot stability ensures that adjustments remain controlled.
Maintenance also includes keeping track of ChromeOS updates. Kernel updates can invalidate previously functioning modules. For this reason, documentation and backup planning are essential components of responsible kernel-level experimentation.
The Role of Containers and Virtualization
Modern Chromebooks support Linux applications through containerization. Crostini, the Linux container environment within ChromeOS, provides user-level Linux functionality without altering the host kernel. Lkmschromebookcheck distinguishes between container-based development and kernel-level modification.
While containers provide significant flexibility, they do not offer direct kernel modification capabilities. Therefore, users seeking hardware-level experimentation may need to move beyond container environments. However, balancing container use with kernel exploration allows users to maintain productivity while experimenting responsibly.
Educational and Professional Applications of Lkmschromebookcheck
The exploration of kernel modules on Chromebooks has educational and professional benefits. Students studying computer science gain insight into operating system architecture by understanding how kernel modules interact with hardware. Professionals in cybersecurity and embedded systems can experiment with low-level components in a controlled environment.
Lkmschromebookcheck positions Chromebooks as more than simple browsing devices. With structured management, they can serve as compact development platforms capable of meaningful experimentation. This transformation broadens the perception of what ChromeOS-based devices can achieve.
Future Outlook for Lkmschromebookcheck and Chromebook Development
As Chromebook hardware becomes more powerful and ChromeOS continues to evolve, the relevance of kernel-level customization may grow. Enhanced processors, improved storage speeds, and expanded developer tools open new possibilities for advanced users.
Lkmschromebookcheck symbolizes a bridge between consumer simplicity and technical depth. While Chromebooks are designed for streamlined use, their Linux foundation ensures that deeper customization remains technically possible. Responsible integration of Loadable Kernel Modules may play a role in shaping the future of Chromebook innovation.
Conclusion
Lkmschromebookcheck highlights the untapped potential within Chromebook systems by exploring the responsible use of Loadable Kernel Modules. By understanding the relationship between ChromeOS and the Linux kernel, users can approach performance optimization, hardware compatibility, and advanced development with clarity and caution. Security, stability, and structured evaluation remain essential pillars of this process.
Chromebooks continue to thrive due to their reliability and ease of use, but for those seeking expanded functionality, kernel-level customization presents an intriguing frontier. Through careful planning and informed experimentation, Lkmschromebookcheck demonstrates how advanced system capabilities can coexist with the streamlined philosophy that defines Chromebook technology.
Technology
Is Skvqx2 the Future? Trends and Predictions for 2026

The digital landscape evolves at a breathtaking pace, and new concepts often emerge that reshape how industries operate. Among these rising innovations, Skvqx2 has started to gain attention as a transformative force in technology, business strategy, and digital infrastructure. As we move closer to 2026, many professionals and analysts are asking a crucial question: Is Skvqx2 the future?
Skvqx2 represents more than just a technological trend; it symbolizes a broader shift toward adaptive systems, integrated automation, and intelligent connectivity. Companies seeking competitive advantage are closely examining how Skvqx2 can enhance efficiency, optimize data usage, and unlock new growth opportunities. With rapid digital adoption across sectors such as finance, healthcare, retail, and manufacturing, the relevance of Skvqx2 continues to expand.
The purpose of this article is to explore whether Skvqx2 truly holds the potential to shape 2026 and beyond. By analyzing trends, market movements, innovation patterns, and predictive insights, we aim to provide a comprehensive outlook on the future direction of this emerging phenomenon.
Understanding Skvqx2 in the Context of Modern Innovation
To evaluate whether Skvqx2 is the future, it is essential to understand what it represents in the broader digital ecosystem. At its core, Skvqx2 can be interpreted as a hybrid innovation framework combining advanced automation, intelligent analytics, and scalable infrastructure. Rather than functioning as a single tool, it acts as an adaptable architecture that integrates with multiple technologies.
The rise of cloud computing, artificial intelligence, machine learning, and blockchain has laid the foundation for systems like Skvqx2. In particular, advancements pioneered by organizations such as OpenAI have demonstrated how intelligent systems can transform industries by enhancing predictive capabilities and automation processes. Similarly, global technology leaders like Microsoft and Google have accelerated the integration of intelligent digital ecosystems.
Skvqx2 operates within this ecosystem by bridging data intelligence with operational scalability. Instead of functioning independently, it enhances connectivity across platforms and enables organizations to automate workflows while maintaining adaptability. This interconnected nature positions it as a potential cornerstone for future digital strategies.
Market Trends Driving the Rise of Skvqx2 in 2026
Several major market trends are contributing to the projected growth of Skvqx2. Digital transformation initiatives have intensified globally, pushing businesses to adopt systems that can streamline operations and reduce manual processes. Organizations are increasingly focused on building resilient digital infrastructures that can adapt to rapid market changes.
Another significant driver is the expansion of remote and hybrid work environments. Businesses require flexible digital frameworks that support seamless collaboration and data access across geographic boundaries. Skvqx2 aligns with these needs by offering integrated systems capable of supporting distributed operations without sacrificing efficiency.
Cybersecurity also plays a crucial role in shaping future technologies. As data breaches become more sophisticated, organizations demand secure and intelligent systems that can monitor and respond to threats in real time. Skvqx2 incorporates predictive analytics, enabling proactive risk mitigation strategies.
The following table outlines key trends influencing its growth trajectory toward 2026:
| Trend Category | Impact on Adoption | Expected Growth by 2026 |
|---|---|---|
| Digital Automation | Increased operational efficiency | High |
| AI Integration | Smarter data insights | Very High |
| Remote Work Infrastructure | Seamless global connectivity | High |
| Cybersecurity Enhancement | Proactive threat detection | Very High |
| Scalable Cloud Systems | Cost-effective expansion | High |
These trends indicate that the environment is highly favorable for systems built on intelligent, integrated frameworks. If Skvqx2 continues aligning with these trends, its influence may significantly expand by 2026.
Technological Innovations Shaping Skvqx2 Development
Innovation remains the backbone of any transformative system. The evolution of Skvqx2 is deeply connected to breakthroughs in artificial intelligence, edge computing, and decentralized networks. Predictive algorithms, real-time data processing, and advanced automation workflows are key components accelerating its adoption.
In 2026, we are likely to see increased integration between Skvqx2 and advanced AI models, similar to those developed within cutting-edge research communities. These integrations may enable faster decision-making, more personalized digital experiences, and optimized supply chain management.
Edge computing is another innovation influencing the future direction of Skvqx2. By processing data closer to its source, organizations can reduce latency and improve performance. This becomes particularly important in industries requiring real-time responsiveness, such as healthcare monitoring systems and smart manufacturing facilities.
Blockchain-based verification systems may also enhance transparency within Skvqx2 frameworks, particularly in financial services and logistics operations. As regulatory environments become more stringent, systems that offer secure, traceable data management will gain a competitive advantage.
Industry Applications and Use Cases for 2026
The potential applications of Skvqx2 span across multiple industries. In finance, predictive analytics can assist in fraud detection and risk assessment. In healthcare, intelligent integration systems can support patient monitoring and operational management. Retail organizations can leverage adaptive frameworks to personalize customer experiences and optimize inventory systems.
Manufacturing industries may use Skvqx2-driven automation to enhance production efficiency and reduce downtime. By connecting machinery, analytics platforms, and predictive maintenance systems, businesses can minimize operational disruptions.
The following table illustrates industry-specific applications projected for 2026:
| Industry | Primary Use Case | Business Outcome |
|---|---|---|
| Finance | Fraud detection and risk analysis | Reduced financial loss |
| Healthcare | Smart patient monitoring | Improved care quality |
| Retail | Personalized shopping systems | Higher customer retention |
| Manufacturing | Predictive maintenance | Lower operational costs |
| Education | Adaptive learning platforms | Enhanced engagement |
These applications demonstrate that Skvqx2 is not confined to one sector. Instead, it represents a versatile framework adaptable to diverse operational requirements.
Challenges That Could Shape the Future of Skvqx2
While optimism surrounds its growth, several challenges could influence whether Skvqx2 truly becomes the future. Regulatory frameworks are evolving rapidly, particularly regarding data privacy and AI governance. Compliance requirements may slow adoption in certain regions.
Cost considerations also remain a barrier for small and medium-sized enterprises. Implementing advanced digital infrastructures requires investment in training, cybersecurity measures, and integration systems. Without accessible pricing models, widespread adoption may face limitations.
Technological complexity is another potential hurdle. Organizations lacking skilled personnel may struggle to fully leverage the capabilities of Skvqx2. Workforce upskilling initiatives will therefore play a significant role in determining its success trajectory.
Despite these challenges, history shows that transformative technologies often overcome early obstacles through adaptation and collaboration. If Skvqx2 continues evolving with regulatory and market expectations, its future may remain promising.
Predictions for Skvqx2 in 2026 and Beyond
Looking ahead to 2026, analysts predict several potential outcomes. First, integration between Skvqx2 and AI-powered systems will likely become more seamless, reducing implementation complexity. Second, subscription-based digital frameworks may make access more affordable for smaller enterprises.
Third, partnerships between technology providers and global enterprises could accelerate innovation cycles. Collaborative ecosystems will enable faster testing, deployment, and refinement of integrated systems.
Additionally, sustainability initiatives may influence development priorities. Energy-efficient infrastructure and environmentally responsible data centers will become critical components of next-generation systems. Skvqx2 frameworks that prioritize sustainability could gain stronger market positioning.
The overall outlook suggests steady expansion rather than overnight dominance. By 2026, Skvqx2 may not fully replace existing systems but could serve as a foundational layer supporting advanced digital operations.
Economic and Global Impact of Skvqx2
From an economic perspective, systems like Skvqx2 can contribute to productivity growth and job market evolution. Automation may streamline repetitive tasks while creating new roles focused on data analysis, system management, and innovation strategy.
Emerging markets may particularly benefit from scalable digital frameworks. Countries investing in digital infrastructure could adopt based systems to accelerate modernization efforts. This global expansion may foster cross-border collaboration and knowledge exchange.
Furthermore, competitive pressure among technology providers will likely drive continuous improvement. Organizations that innovate responsibly and prioritize ethical AI practices will shape how Skvqx2 evolves within the global marketplace.
Conclusion
The question of whether Skvqx2 is the future depends largely on how effectively it adapts to technological advancements, regulatory shifts, and market demands. Current trends indicate strong growth potential fueled by automation, artificial intelligence, cybersecurity enhancement, and scalable digital infrastructure.
By 2026, Skvqx2 may become a central element of digital transformation strategies across multiple industries. While challenges such as cost, compliance, and workforce readiness remain, the trajectory suggests increasing adoption rather than decline.
Ultimately, the future of Skvqx2 will be shaped by innovation, collaboration, and strategic implementation. If organizations leverage its capabilities responsibly and continue investing in adaptive digital ecosystems, could indeed represent a defining framework of the next generation of technological progress.
Technology
Password makesilver2121: Password Strength and Security

In today’s rapidly evolving digital world, the concept of Password makesilver2121 serves as a powerful reminder of how critical password strength and security have become. From social media accounts to online banking platforms, passwords are the first and often only line of defense between personal data and cyber threats. Weak credentials can lead to identity theft, financial loss, and unauthorized access to sensitive information. Understanding the principles behind secure authentication practices helps individuals and organizations build a safer digital presence. This article explores password security in depth, explaining how strong authentication works, why it matters, and how to implement effective strategies without compromising convenience.
Password makesilver2121 and the Foundation of Digital Security
The phrase Password makesilver2121 symbolizes more than just a combination of characters. It represents the foundation of digital protection in a connected environment. Every online service, whether it is email, cloud storage, or e-commerce, relies on password-based authentication as the first checkpoint. Without a strong barrier, systems remain vulnerable to cybercriminals who exploit predictable patterns and reused credentials.
Digital security begins with awareness. Many users underestimate the importance of complex passwords because they prioritize memorability over protection. However, cyber attackers use automated tools capable of testing millions of combinations within seconds. A weak password can be cracked almost instantly. This reality makes strong password practices essential rather than optional.
Organizations worldwide invest heavily in cybersecurity infrastructure, yet individual password hygiene remains a decisive factor. A robust authentication strategy combines strong credentials with additional layers of verification to reduce risks significantly. Understanding how these systems work empowers users to take control of their digital security.
Password makesilver2121 and Understanding Password Strength
Password makesilver2121 emphasizes the importance of strength in authentication. Password strength refers to how resistant a password is to guessing or brute-force attacks. Several factors determine strength, including length, complexity, unpredictability, and uniqueness.
Longer passwords are exponentially harder to crack. Each additional character increases the number of possible combinations, making automated attacks more time-consuming and resource-intensive. Complexity also plays a vital role. A mixture of uppercase letters, lowercase letters, numbers, and symbols significantly improves resilience against dictionary attacks.
Unpredictability is equally important. Common words, birthdates, and simple sequences are easily guessed. Cybercriminals often rely on leaked databases of frequently used passwords to attempt credential stuffing attacks. Unique combinations reduce this risk dramatically.
The following table illustrates how password length impacts security in theoretical brute-force scenarios.
| Password Length | Possible Combinations | Estimated Crack Time (Basic Attack) |
|---|---|---|
| 6 characters | Millions | Seconds to minutes |
| 8 characters | Billions | Minutes to hours |
| 12 characters | Trillions | Years |
| 16 characters | Quadrillions | Centuries |
This comparison demonstrates why increasing password length is one of the most effective security strategies. The difference between eight and twelve characters can determine whether an account remains safe or becomes compromised.
Password makesilver2121 and Common Security Threats
Password makesilver2121 highlights the importance of recognizing threats that target weak credentials. Cybercriminals employ various techniques to exploit password vulnerabilities. Phishing remains one of the most common methods. In phishing attacks, users receive fraudulent emails or messages that mimic legitimate organizations, tricking them into revealing login details.
Brute-force attacks involve automated systems attempting numerous combinations until the correct one is found. Although modern systems often limit repeated attempts, weak passwords remain vulnerable. Credential stuffing is another significant threat. Attackers use stolen login information from one website to access accounts on other platforms, exploiting users who reuse passwords.
Malware-based keylogging is also a growing concern. Malicious software records keystrokes, capturing sensitive information silently. These threats demonstrate why relying solely on a simple password is insufficient in today’s digital environment.
Password makesilver2121 and the Role of Multi-Factor Authentication
Password makesilver2121 encourages the integration of additional security layers. Multi-factor authentication, commonly abbreviated as MFA, adds extra verification steps beyond a password. This approach significantly reduces the risk of unauthorized access even if credentials are compromised.
MFA typically combines three categories of authentication factors. The first is something you know, such as a password. The second is something you have, like a smartphone receiving a verification code. The third is something you are, such as biometric identification including fingerprints or facial recognition.
The following table explains how different authentication factors enhance security.
| Authentication Factor | Example | Security Benefit |
|---|---|---|
| Knowledge | Password | Basic access control |
| Possession | SMS code | Confirms device ownership |
| Inherence | Fingerprint | Biometric verification |
By combining these elements, systems create multiple barriers against unauthorized access. Even if one layer fails, additional verification protects the account.
Password makesilver2121 and Password Management Tools
Password makesilver2121 also underscores the importance of proper credential management. Many users struggle to remember complex passwords for multiple accounts. This challenge often leads to risky practices such as reusing the same password across platforms.
Password managers offer a practical solution. These tools generate and store strong, unique passwords securely. Instead of memorizing numerous combinations, users only need to remember one master password. Encrypted storage ensures that sensitive data remains protected.
Modern password managers also provide features such as automatic password updates, breach monitoring, and secure sharing options. These functionalities simplify the process of maintaining strong authentication practices without sacrificing convenience.
Password makesilver2121 and Creating Strong Passphrases
Password makesilver2121 promotes the concept of passphrases as an alternative to short, complex passwords. A passphrase consists of a sequence of random words that form a long yet memorable combination. For example, combining unrelated words with numbers and symbols can create highly secure credentials.
Passphrases provide both length and unpredictability. Since they are longer than traditional passwords, they are more resistant to brute-force attacks. At the same time, they are easier to remember than random strings of characters.
Research indicates that length contributes more to security than complexity alone. A long passphrase containing simple words may outperform a short, complex password in many scenarios. This approach encourages users to adopt stronger authentication habits without frustration.
Password makesilver2121 and Organizational Security Policies
Password makesilver2121 reflects the importance of structured security policies within organizations. Businesses face greater risks because they manage sensitive data such as customer information, financial records, and proprietary content. Weak employee passwords can lead to large-scale breaches.
Effective organizational policies include mandatory password length requirements, enforced periodic updates, and the use of MFA. Security training also plays a critical role. Employees must understand phishing risks and recognize suspicious communication.
Companies often implement password rotation policies to minimize exposure. However, modern security experts suggest that forced frequent changes may encourage weaker patterns. Instead, focusing on strong initial creation and monitoring for breaches provides a more balanced approach.
Password makesilver2121 and Encryption Technology
Password makesilver2121 connects directly to encryption practices. When users create passwords, secure systems do not store them in plain text. Instead, they use hashing algorithms to convert credentials into encrypted formats. Hashing ensures that even if databases are compromised, original passwords remain protected.
Advanced systems use salted hashes, which add random data before encryption. This technique prevents attackers from using precomputed tables to reverse-engineer passwords. Encryption standards continue evolving to counter increasingly sophisticated threats.
Understanding how encryption works builds trust in digital services and encourages users to adopt best practices confidently.
Password makesilver2121 and Future Authentication Trends
Password makesilver2121 also opens discussion about the future of authentication. While passwords remain central to digital security, emerging technologies aim to reduce reliance on traditional credentials. Biometric authentication, hardware security keys, and passwordless systems are gaining popularity.
Passwordless authentication uses cryptographic keys stored on trusted devices. Instead of typing a password, users verify identity through secure tokens or biometrics. This method reduces phishing risks and simplifies the login experience.
Despite these advancements, passwords are unlikely to disappear completely in the near future. Instead, hybrid systems combining traditional and modern authentication methods will dominate cybersecurity strategies.
Password makesilver2121 and Personal Responsibility in Cybersecurity
Password makesilver2121 ultimately emphasizes individual responsibility. Technology alone cannot guarantee protection. Users must adopt proactive habits such as updating software regularly, avoiding suspicious links, and using secure networks.
Cybersecurity is a shared responsibility between service providers and users. While companies implement encryption and monitoring systems, individuals must maintain strong credentials and remain vigilant against threats.
The following table summarizes key practices for maintaining secure authentication.
| Security Practice | Purpose | Impact |
|---|---|---|
| Use long passwords | Increase resistance to brute-force attacks | High |
| Enable MFA | Add extra verification layer | Very High |
| Avoid reuse | Prevent credential stuffing | High |
| Use password manager | Simplify strong password storage | High |
These strategies collectively reduce vulnerability and enhance overall digital resilience.
Password makesilver2121 and Building a Secure Digital Future
Password makesilver2121 represents more than a phrase. It symbolizes awareness, discipline, and commitment to digital safety. As cyber threats grow more sophisticated, strong authentication practices remain essential for protecting personal and professional information.
The digital landscape continues expanding, connecting billions of devices and users worldwide. Each connection introduces potential vulnerabilities. By prioritizing password strength, leveraging multi-factor authentication, and adopting modern security tools, individuals and organizations can minimize risks effectively.
A secure digital future depends on education and consistent action. Strong passwords are not merely technical requirements; they are protective shields safeguarding identities, finances, and reputations. Embracing best practices today ensures greater protection tomorrow.
Technology
Betechit. com: Shaping the Future of Technology Blogging

In a rapidly evolving digital world where information travels faster than ever, Betechit. com emerges as a dynamic platform redefining how technology news, insights, and analysis are delivered to global readers. Technology blogging has moved far beyond simple gadget reviews and product announcements; it now demands deep research, authentic storytelling, and meaningful engagement. This transformation has opened the door for innovative platforms that combine credibility, creativity, and clarity. Among these, Betechit. com stands out as a modern voice that reflects both industry expertise and reader-centric values.
The future of technology blogging lies in personalization, data-driven storytelling, and ethical reporting. Platforms that succeed are those that understand their audience and consistently adapt to changing trends. As artificial intelligence, cybersecurity, fintech, blockchain, cloud computing, and sustainable technologies continue to reshape industries, technology blogs must evolve alongside them. The responsibility extends beyond publishing information; it includes shaping conversations and influencing how innovation is understood by society.
The Vision Behind Betechit. com
Every successful digital platform begins with a vision. The driving force behind Betechit. com is to create a reliable digital environment where technology enthusiasts, professionals, and entrepreneurs can access well-structured and forward-thinking content. The platform is built on the idea that technology should be explained clearly without sacrificing complexity.
The vision centers on three interconnected pillars: credibility, accessibility, and innovation. Credibility ensures that published content is thoroughly researched and fact-checked. Accessibility guarantees that complex technical concepts are translated into language that readers from diverse backgrounds can understand. Innovation reflects the commitment to covering emerging trends before they become mainstream topics.
Modern readers expect transparency. They value insights supported by data rather than assumptions. This platform’s editorial framework prioritizes structured research, expert commentary, and comparative analysis. By integrating storytelling techniques with factual depth, it transforms technical discussions into engaging narratives.
The following table illustrates the foundational pillars that guide the platform’s strategic direction.
| Core Pillar | Strategic Focus | Long-Term Impact |
|---|---|---|
| Credibility | Research-driven articles and expert validation | Builds trust and authority |
| Accessibility | Clear explanations and simplified terminology | Expands audience reach |
| Innovation | Early coverage of emerging technologies | Positions platform as industry thought leader |
The alignment of these pillars ensures that the platform does not merely report trends but interprets them in a meaningful way.
Content Strategy at Betechit. com
Content strategy defines how a technology blog differentiates itself in a crowded marketplace. The approach adopted at Betechit. com revolves around depth, structure, and consistency. Instead of chasing viral trends alone, the focus remains on producing evergreen content that maintains long-term relevance.
Long-form articles dominate the editorial calendar. These pieces explore subjects such as artificial intelligence ethics, cloud infrastructure optimization, digital marketing automation, green computing, and data privacy regulations. By offering comprehensive guides, the platform positions itself as a reference source rather than a fleeting news outlet.
The strategy also integrates comparative analysis. Readers appreciate structured comparisons when evaluating software tools, cybersecurity frameworks, or development environments. Clear tables within articles improve readability and support data-driven decisions.
Below is an example of how structured comparisons enhance clarity within content.
| Technology Trend | Current Adoption Level | Growth Projection | Industry Impact |
|---|---|---|---|
| Artificial Intelligence | High | Rapid | Transformative |
| Blockchain Applications | Moderate | Expanding | Disruptive |
| Cloud Computing | Very High | Stable Growth | Foundational |
| Green Technology | Emerging | Accelerating | Sustainable |
By embedding such structured insights within narratives, articles remain both analytical and approachable.
Another key aspect of the strategy is editorial consistency. Publishing schedules follow a well-defined timeline that ensures readers can anticipate fresh content. This builds loyalty and repeat engagement. Consistency also improves search engine trust, contributing to long-term visibility.
Innovation and Community at Betechit. com
Innovation in technology blogging extends beyond content topics. It includes user experience design, interactive elements, and audience engagement strategies. Betechit. com integrates responsive design principles to ensure seamless access across devices, recognizing that a large percentage of users browse content through smartphones and tablets.
Community building forms another critical dimension. Instead of functioning as a one-directional broadcasting channel, the platform encourages dialogue. Comment sections, reader surveys, and collaborative guest posts create an interactive ecosystem. This fosters knowledge exchange between writers and readers.
The digital community benefits from transparency in editorial voice. Articles maintain neutrality while presenting balanced viewpoints. When discussing emerging technologies such as machine learning automation or decentralized finance, content highlights both opportunities and potential risks. This balanced approach strengthens reader trust.
Data analytics further enhances innovation. Monitoring reader behavior provides insights into engagement patterns, preferred topics, and reading duration. This information supports continuous improvement in content structure and topic selection. The integration of analytics does not compromise privacy; instead, it supports strategic refinement while respecting user data.
A structured view of engagement strategies demonstrates how community interaction contributes to growth.
| Engagement Method | Purpose | Expected Outcome |
|---|---|---|
| Interactive Comments | Encourage discussion | Increased user retention |
| Expert Interviews | Provide authority-backed insights | Enhanced credibility |
| Data Analytics Review | Optimize content performance | Improved content relevance |
| Guest Contributions | Diversify perspectives | Broader audience appeal |
By aligning innovation with community involvement, the platform nurtures a sustainable digital ecosystem.
SEO Philosophy of Betechit. com
Search engine optimization remains a critical element in digital publishing. However, the philosophy at Betechit. com prioritizes organic readability over aggressive keyword repetition. Modern search algorithms reward quality, context, and semantic richness rather than mechanical density.
The SEO framework focuses on structured headings, natural keyword placement, internal linking logic, and mobile optimization. Instead of forcing repetitive phrases, the strategy embraces topic clusters. This method organizes related articles under comprehensive themes, strengthening topical authority.
For instance, an article discussing cybersecurity might internally connect to related pieces covering encryption standards, data breach case studies, and privacy compliance frameworks. Such internal linking enhances both user navigation and search engine indexing.
Technical SEO components also play a role. Fast loading speed, optimized images, clean URL structures, and schema markup collectively improve performance. Below is a simplified representation of technical optimization elements integrated into the platform’s workflow.
| SEO Element | Implementation Focus | Performance Benefit |
|---|---|---|
| Page Speed | Image compression and caching | Reduced bounce rate |
| Structured Data | Schema markup integration | Enhanced search visibility |
| Internal Linking | Topic cluster organization | Stronger authority signals |
| Mobile Optimization | Responsive design | Improved user experience |
This balanced SEO approach ensures long-term visibility without sacrificing authenticity or readability.
Beyond algorithms, the philosophy emphasizes value-driven writing. Articles are crafted to answer real questions rather than manipulate rankings. This alignment between reader satisfaction and search engine standards strengthens sustainability.
Technology Coverage and Editorial Depth
A defining characteristic of a forward-thinking technology blog is the diversity of its coverage. Topics span across artificial intelligence, blockchain ecosystems, cybersecurity innovations, cloud infrastructure, digital marketing technologies, and sustainable computing. Each subject receives contextual analysis rather than superficial commentary.
Artificial intelligence coverage explores not only automation tools but also ethical implications and regulatory developments. Blockchain discussions move beyond cryptocurrency headlines to examine supply chain transparency and decentralized identity frameworks. Cybersecurity reporting emphasizes proactive defense strategies instead of reactive incident summaries.
Editorial depth is achieved through layered research. Articles integrate statistical data, industry case studies, and predictive insights. By examining both historical context and future projections, content delivers a holistic understanding of technological shifts.
The integration of narrative storytelling strengthens engagement. Instead of presenting raw data alone, articles contextualize information within real-world scenarios. For example, a discussion about remote work technologies might analyze how cloud collaboration tools transformed workplace productivity during global disruptions.
This combination of data and narrative fosters emotional resonance while maintaining analytical rigor.
The Future Roadmap of Betechit. com
Looking ahead, Betechit. com envisions expansion into multimedia storytelling, including podcasts, video explainers, and interactive webinars. Diversification of content formats reflects changing consumption habits. Modern readers often alternate between reading long-form articles and watching short explainer videos.
The roadmap also includes expanding global perspectives. Technology innovation is no longer concentrated in a few regions; emerging markets are contributing groundbreaking solutions. By featuring international voices, the platform strengthens diversity and inclusivity.
Sustainability will remain a priority theme. As climate concerns intensify, green technology innovations demand deeper coverage. From energy-efficient data centers to eco-friendly hardware manufacturing, environmental responsibility intersects strongly with technological progress.
Artificial intelligence-assisted research tools may support editorial workflows while maintaining human oversight. Automation can streamline data analysis, but human writers preserve creativity, ethical judgment, and contextual interpretation. This synergy between automation and authenticity defines the next phase of digital publishing.
The future vision aligns with measurable objectives.
| Future Initiative | Strategic Objective | Expected Impact |
|---|---|---|
| Multimedia Expansion | Diversify content formats | Higher audience engagement |
| Global Contributor Base | Increase international perspectives | Broader market reach |
| Sustainability Focus | Highlight eco-friendly innovation | Strengthened social responsibility |
| AI-Assisted Research | Improve efficiency and accuracy | Faster content production |
Through careful planning and adaptive strategy, the platform continues to refine its identity while responding to technological evolution.
Building Trust in a Rapidly Changing Industry
Trust is the currency of digital publishing. In an era where misinformation spreads rapidly, credibility distinguishes reputable platforms from unreliable sources. Transparency in sourcing, acknowledgment of limitations, and balanced analysis are critical components of sustainable growth.
Readers are increasingly aware of bias and promotional influence. Maintaining editorial independence strengthens reputation. Sponsored collaborations, when present, must be clearly disclosed to preserve integrity. Ethical journalism practices create a stable foundation for long-term success.
Consistency in tone and style further enhances trust. Articles maintain clarity without sensationalism. Predictions are framed as projections rather than guaranteed outcomes. By avoiding exaggerated claims, the platform cultivates realistic expectations.
As technology continues to reshape industries, reliable interpretation becomes invaluable. Businesses rely on accurate information to guide investments. Professionals depend on credible insights to refine skills. Students seek understandable explanations to support learning. Serving these diverse needs requires discipline, research, and adaptability.
Conclusion
Technology blogging stands at the intersection of innovation, communication, and education. Platforms that succeed in this competitive space are those that combine research-driven depth with reader-friendly clarity. By prioritizing credibility, structured SEO strategies, community engagement, and forward-looking analysis, Betechit. com exemplifies how digital publishing can evolve responsibly.
The future of technology blogging belongs to platforms that embrace transparency, innovation, and sustainability. Through thoughtful expansion into multimedia, global collaboration, and ethical reporting, this model demonstrates how digital media can inform, inspire, and influence audiences worldwide. As technology accelerates, the need for trustworthy interpretation will only grow stronger, ensuring continued relevance for platforms that remain adaptable and authentic.
-
 Blog2 weeks ago
Blog2 weeks agoSimpcit6: Redefining Simplicity in a Complex World
-
 Technology5 months ago
Technology5 months agoYourAssistantLive com: The Future of Smart Digital Assistance
-

 food5 months ago
food5 months agoCalamariere: How to Perfectly Prepare at Home
-
 Blog5 months ago
Blog5 months agoBaddi Hub: An Emerging Industrial and Business Hotspot
-

 Health4 months ago
Health4 months agoNerovet AI Dentistry: Enhancing Patient Experience and Treatment Outcomes Dental Care
-

 Technology2 weeks ago
Technology2 weeks agoVoomixi com: The Digital Platform Redefining Online Interaction
-

 Crypto5 months ago
Crypto5 months agoCrypto30x.com vs Other Crypto Sites – Best Bitcoin Tools?
-
 Lifestyle2 weeks ago
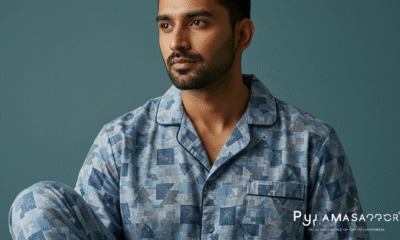
Lifestyle2 weeks agoPyjamaspapper: The Ultimate Blend of Comfort and Style in Sleepwear
